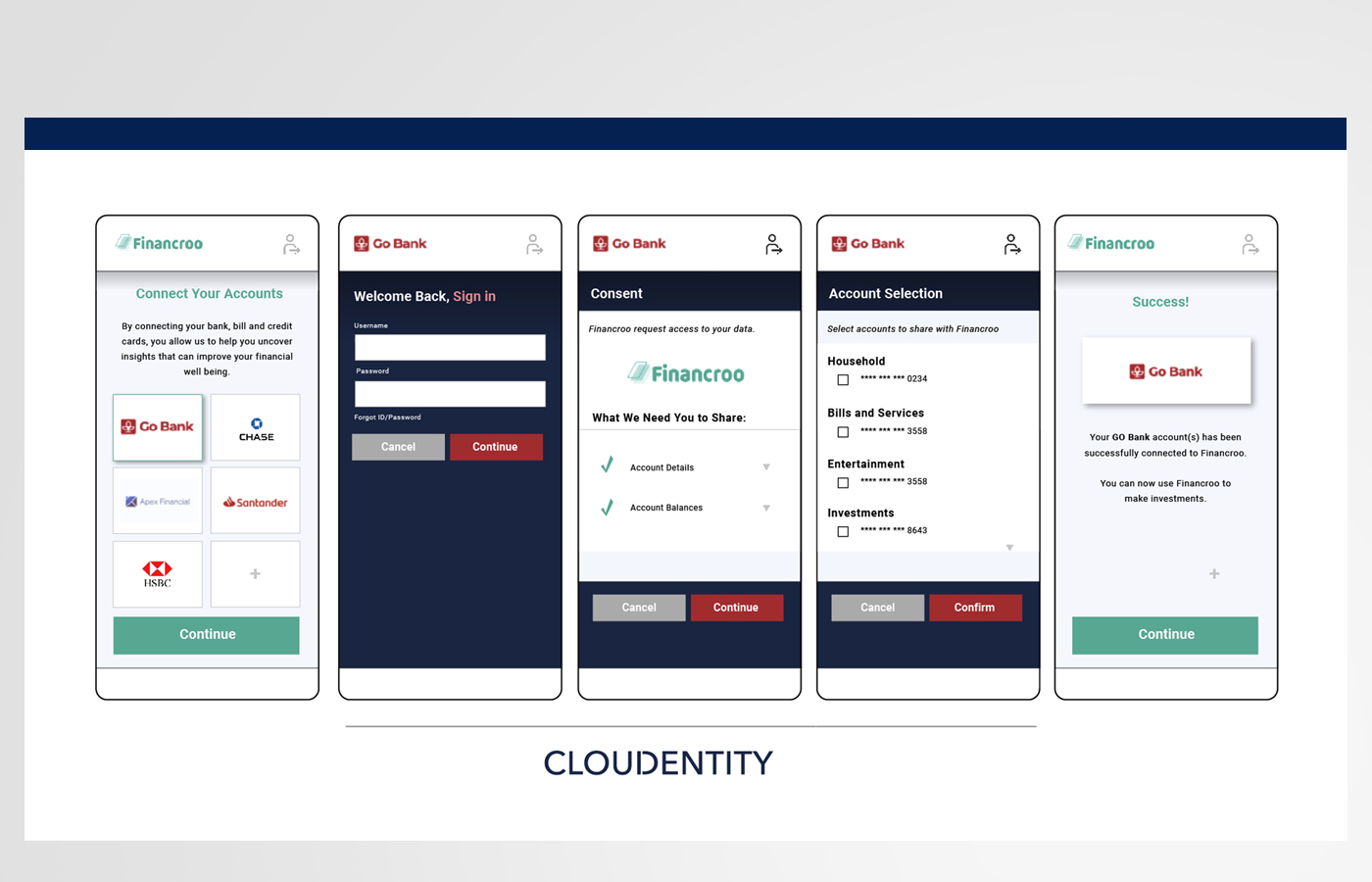
Cloudentity
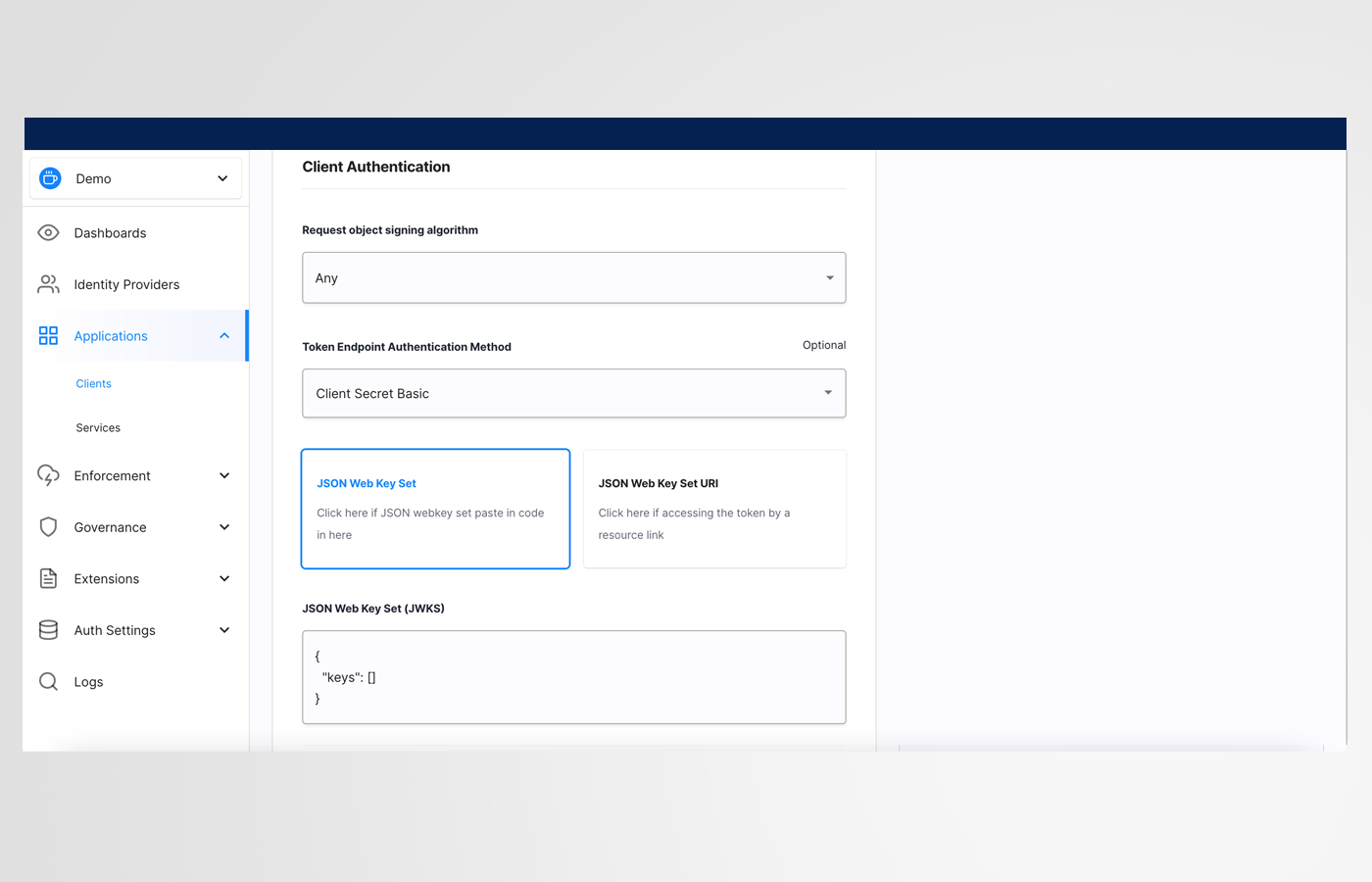
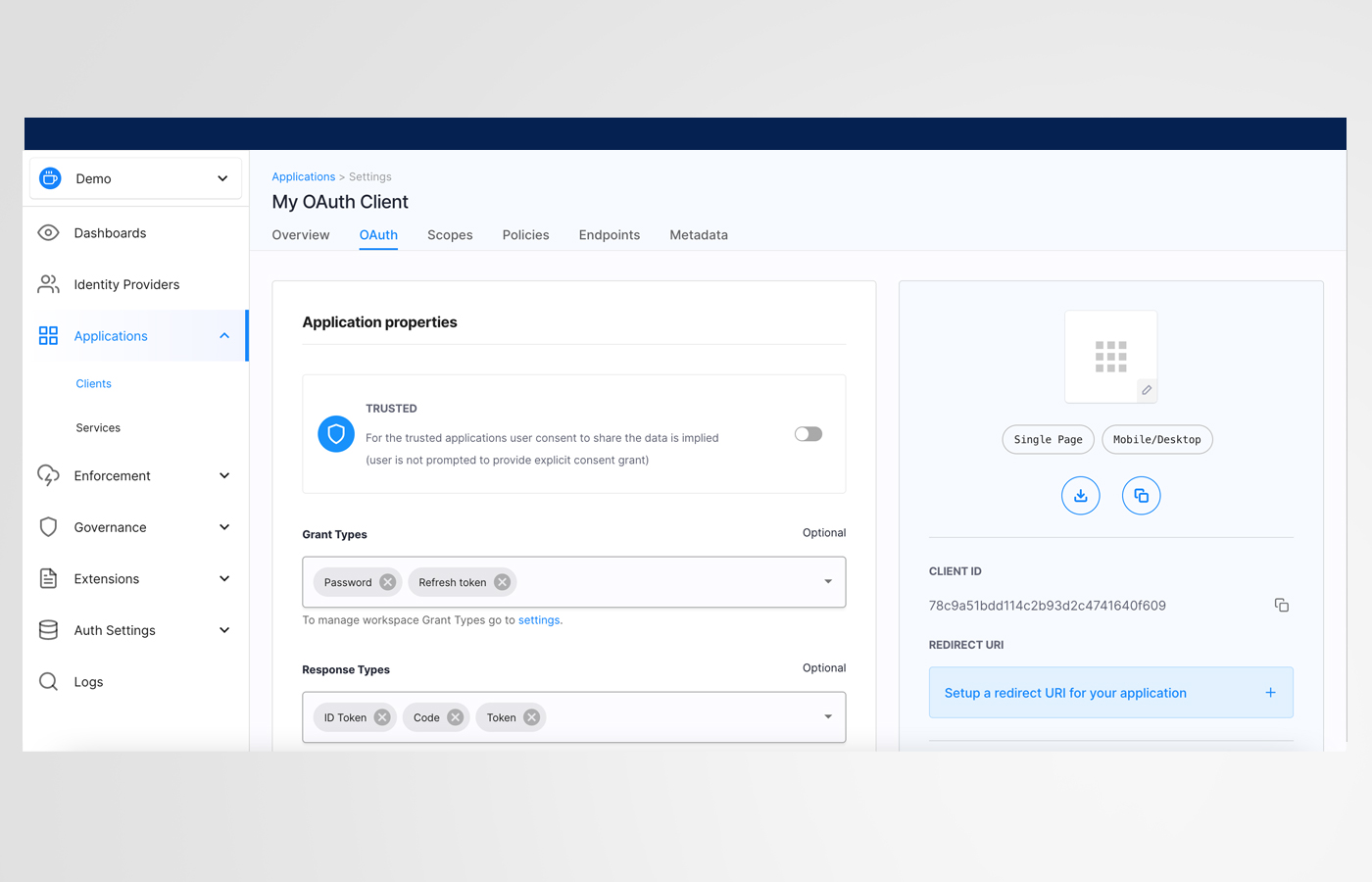
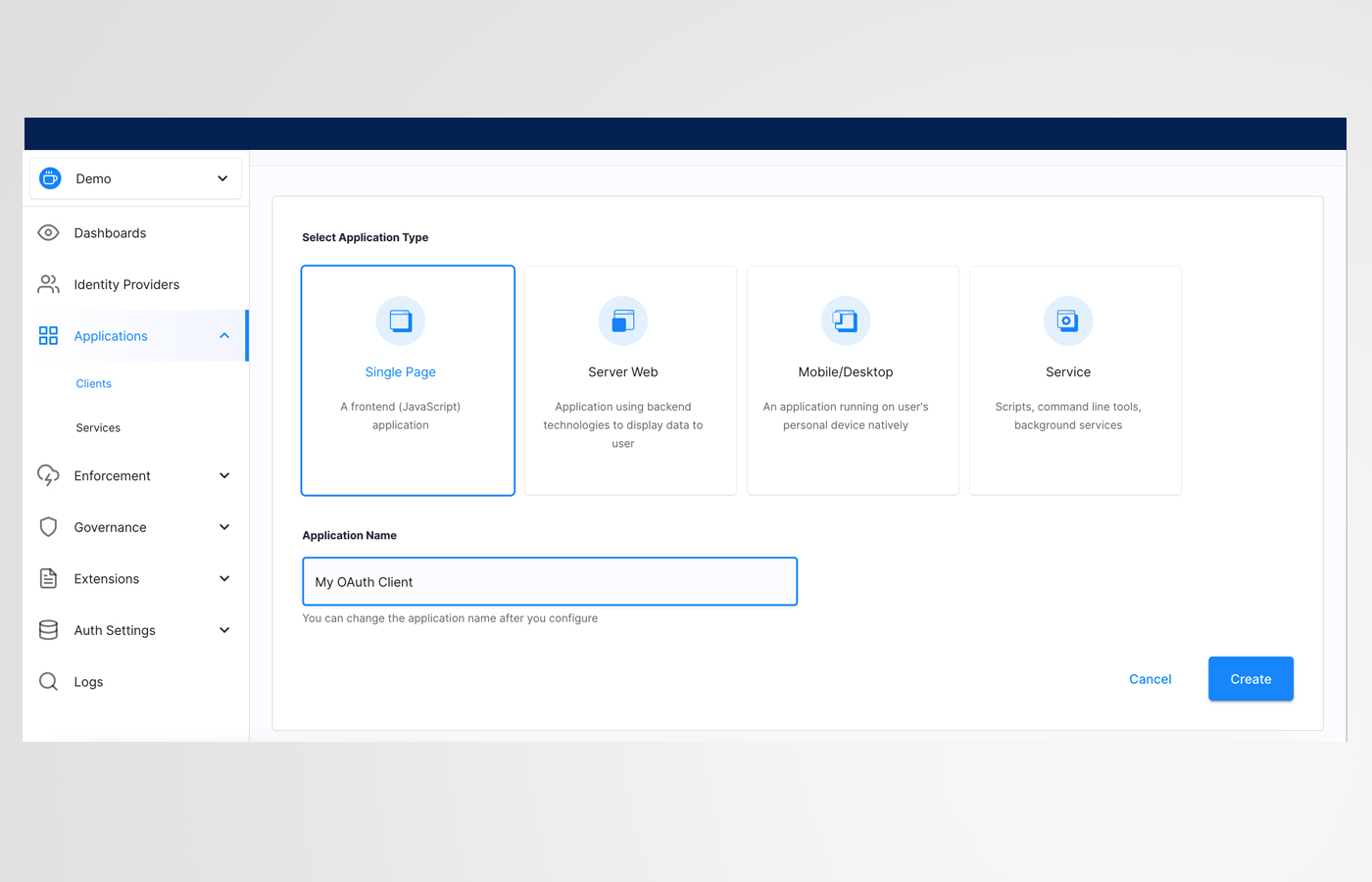
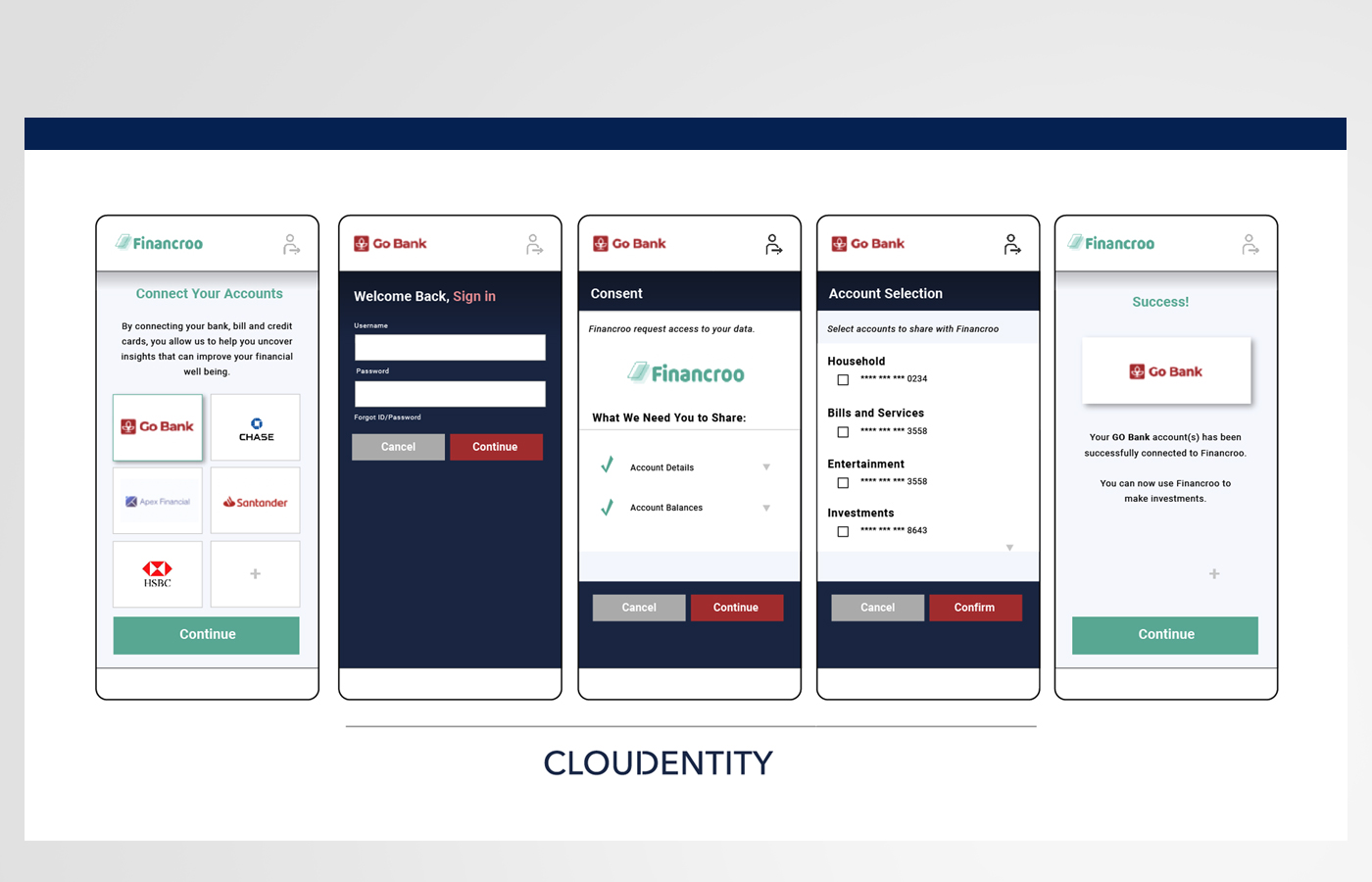
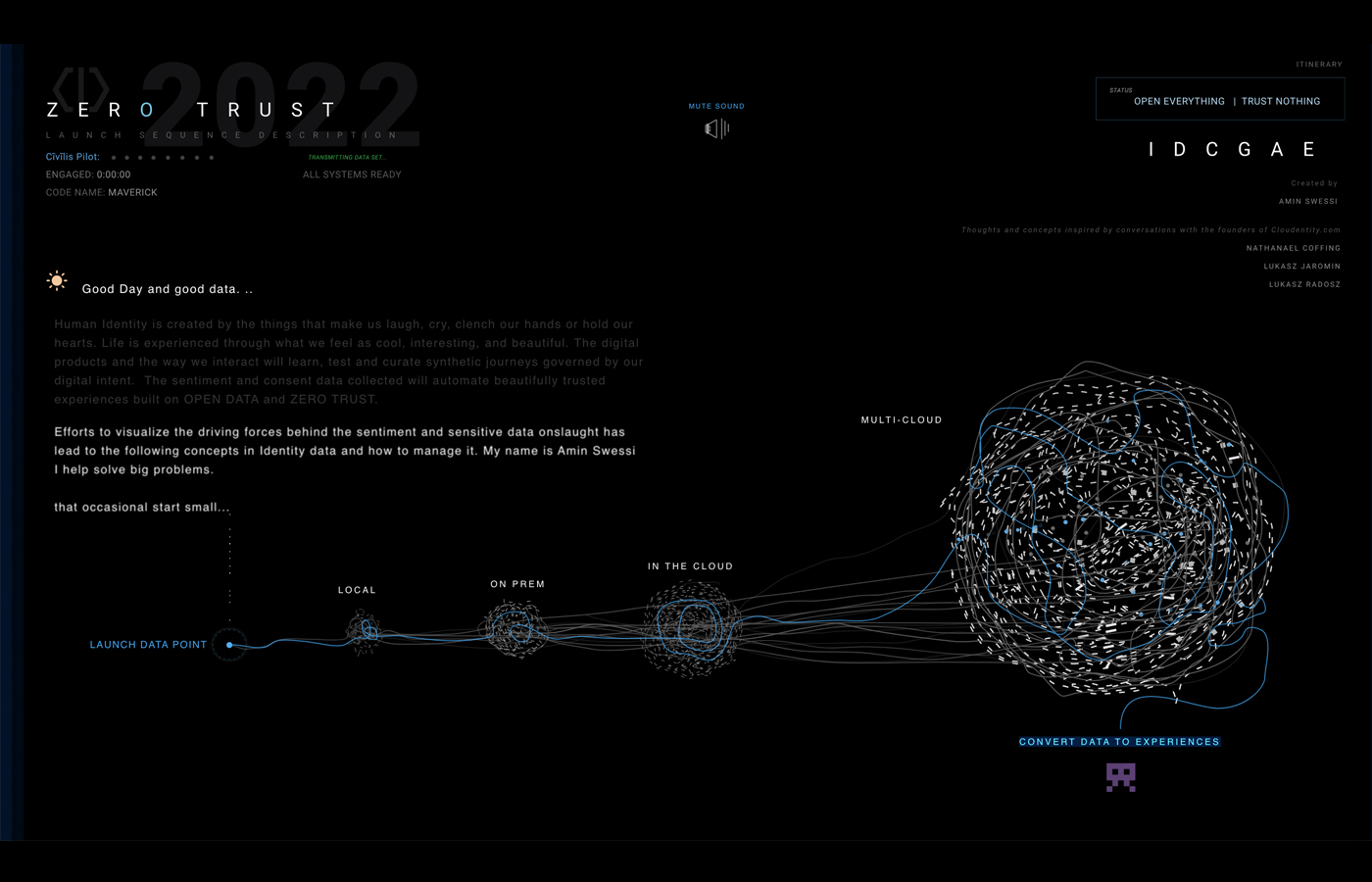
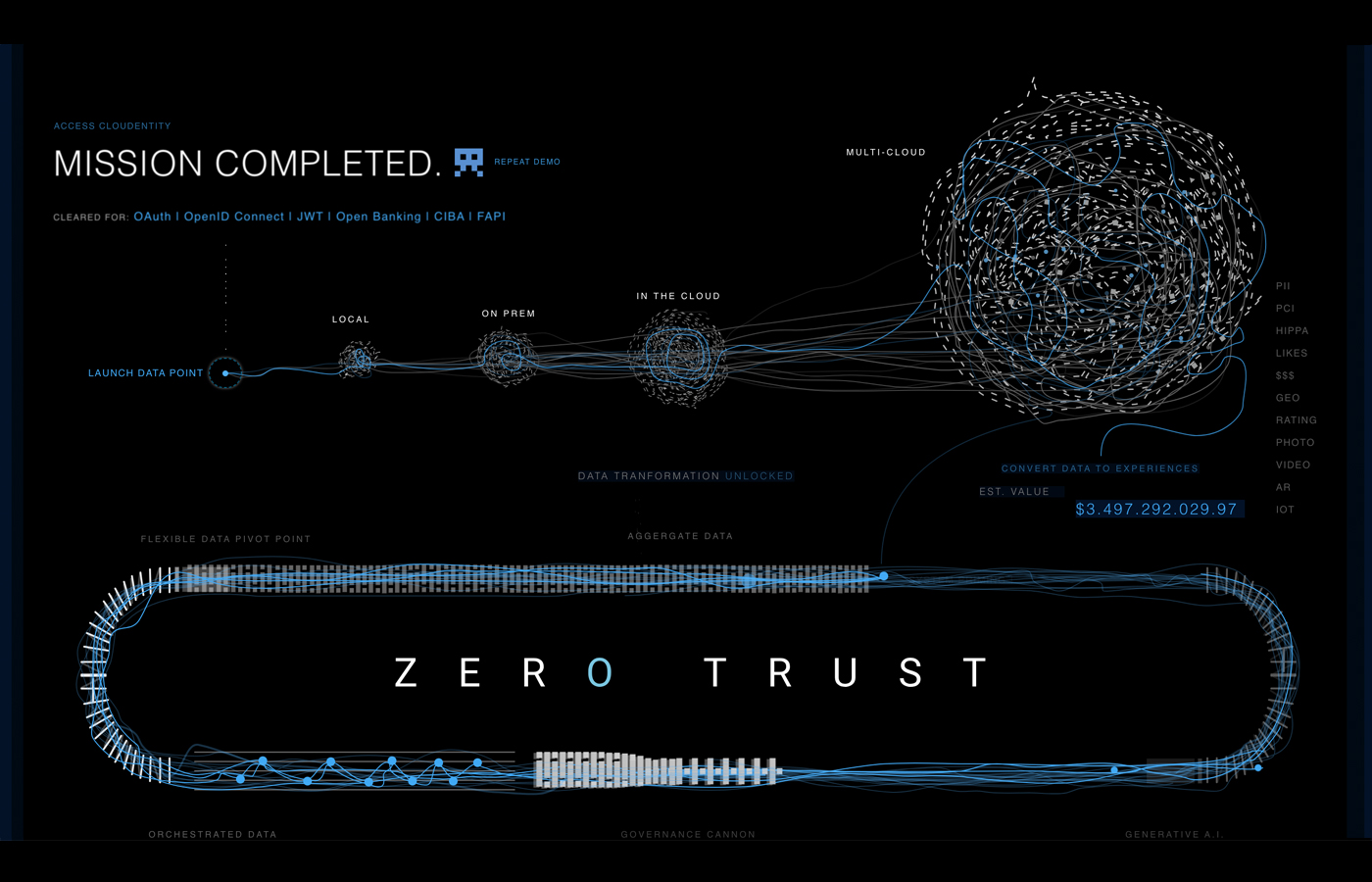
Founder-level product design for a cloud-native identity & authorization control planeCloudentity was built for the “open everything, trust nothing” era: hybrid cloud, API-first ecosystems, and modern identity architectures where authorization, consent, and auditability can’t be bolted on at the end. My work centered on designing a scalable product foundation—workflows, information architecture, and system patterns—that supported high-velocity engineering while keeping the experience coherent for security leadership, platform teams, and developers shipping to production.